Article Content
1 Introduction
With the rapid advancement of technology, the number of images is increasing day by day. As new structures emerge, such as the way images are obtained, their formats, and sizes, the processing of these images becomes more complex. At this point, new image encryption algorithms are needed to ensure the security of these images (Gao et al. 2022a; Muhammad and Özkaynak 2021). Because we live in the information age, people use data all the time. Many security problems occur during this use. In recent years, the use of images has become widespread, especially on the internet. For images to be transmitted securely over insecure networks, they must be encrypted with a strong algorithm (Artuğer and Özkaynak 2021). Especially with the rapid development of chaotic dynamics, progress in this field has accelerated. Because chaotic dynamics are one of the indispensable building blocks of the cryptography field due to their randomness. Encryption philosophies are generally examined under two headings. These are symmetric and asymmetric algorithms. Asymmetric encryption algorithms are not generally used in the encryption process because they are inherently slow. They are mostly used for key exchange. Symmetric encryption algorithms are the philosophy often used for encryption. This philosophy is divided into two. These are stream and block ciphers. In stream encryption, bits are encrypted one by one. Therefore, it is difficult to implement in some cases. Especially as the data increases, its application becomes more difficult. Because it is necessary to generate a key as long as the data size. The other and most used structure for encryption is the block encryption philosophy. These algorithms divide the data into blocks and encrypt each block within itself. Then, these encrypted blocks are combined to obtain encrypted data. Many block cipher algorithms have been developed from the past to the present. The most well-known of these and today’s data encryption standard is the AES (Daemen and Rijmen 1998) algorithm. AES is a secure algorithm with a very flexible structure. However, new algorithms are also needed for various applications.
Image encryption is a very popular topic. Two criteria must be met in the encryption process. The first of these is the process called diffusion. Diffusion means that data must be spread effectively. In this way, the attackers’ job will become even more difficult. In encryption algorithms, this criterion is usually met by permutation operations. In this study, this process is achieved by randomly obtained permutations. The other and most important criterion is the criterion called confusion. This criterion must be met in an encryption algorithm. Confusion means that data must be mixed effectively. The more effectively data is scrambled, the harder it will be for attackers to decipher. That’s why the confusion criterion is vital in an encryption algorithm. When looking at the literature, XOR operation and s-box structures are generally used in the confusion process. The XOR process has a perfect structure for the mixing process, as 50% of the results are 1 and 50% are 0. In this way, it is a structure that makes it very difficult for attackers to make inferences. XOR operation was also used in this study. Another confusion tool is s-box structures, and this structure is generally used. Since S-box is a non-linear transformation, it converts the data into another format. That is, the strength of encryption algorithms generally depends on the strength of the s-box structure. Developing an S-box is a very popular topic today. However, developing strong s-box structures is a very difficult problem. From past to present, to develop strong s-box structures to be used in encryption algorithms, chaos (Lambić 2020; Artuğer and Özkaynak 2020, 2023a; Belazi and Abd El-Latif 2017; Khan et al. 2012, 2013; Alshekly et al. 2022; Ye and Zhimao 2018; Liu 2017; Özkaynak 2020), mathematical transformations (Hussain 2020; Razaq et al. 2022, 2021; Siddiqui et al. 2020; Anees and Chen 2020; Ahmad and Al-Solami 2020a; Khan and Shah 2014; Arshad et al. 2022; Malik et al. 2020), optimization techniques (Behera and Gangopadhyay 2023; Artuğer and Özkaynak 2022, 2023b; Wang et al. 2012, 2020; Zamli 2021; Zamli et al. 2021, 2023; Kuznetsov et al. 2023; Khan et al. 2021, 2023; Artuğer 2023a; Alhadawi et al. 2020, 2021; Ahmad and Al-Solami 2020b; Ahmad et al. 2015, 2020; Hematpour and Ahadpour 2021; Alzaidi et al. 2018; Ahmed et al. 2019; Chen 2008; Farah et al. 2017; Tian and Lu 2017), cellular automata (Szaban and Seredynski 2008; Alexan et al. 2022; Gangadari and Ahamed 2018; Aboytes-González et al. 2018; Haque et al. 2022; Mariot et al. 2019), DNA-RNA chains. Many algorithms have been developed, especially (Artuğer 2023b; Al-Wattar et al. 2015a, b; Basha et al. 2022; Kadhim et al. 2016; Farhan et al. 2020; Mohamed et al. 2021). In this study, three different strong chaos-based s-box structures were used in the confusion process. These s-box structures were obtained uniquely.
Especially in recent years, many image encryption algorithms have been developed. Some of these are briefly mentioned here. Gao et al. They propose a fast image encryption algorithm using propagation, a chaotic system, and shuffling (Gao et al. 2022a). Elkandoz et al. They first shuffled the pixels of the image to meet the mixing and spreading criteria. Then, they effectively encrypted the image by XORing the key value with this mixed data (Elkandoz and Alexan 2022). Alexan et al. They proposed a new image encryption scheme based on the fusion of multiple chaotic maps. The key value was also obtained with the chaotic map (Alexan et al. 2023a). Lai et al. They first proposed a new chaotic map for effective encryption of images. They claimed that this map gave better results compared to other maps. In the proposed encryption method, pixels are based on the philosophy of spreading randomly. As a result, it was observed because of the analysis that the study worked effectively (Lai et al. 2023). Chai et al. They presented a hybrid approach by using the Hessenberg decomposition-block compression detection-particle swarm optimization algorithm together to develop an effective image encryption scheme. As a result of the analysis, it was shown that the algorithm works effectively (Chai et al. 2022). Gao et al. They developed a new image encryption mechanism using a three-dimensional cube and a hyperchaotic map. Later, they made the algorithm more effective by using the DNA coding structure. Analysis has shown that this algorithm is safe (Gao et al. 2022b). Erkan et al. To develop a powerful image encryption algorithm, they first developed a new two-dimensional hyperchaotic map. Analyzes have shown that this map has strong random properties and can be used for image encryption (Erkan et al. 2023). Muhammad et al. They developed a hybrid scheme for image encryption by using optimization algorithms, chaotic systems, and PUF structures together. Effective results were obtained by using these structures together (Muhammad and Özkaynak 2021). Alexan et al. They developed a new image encryption scheme based on hyperchaotic maps and a neuron model. In this study, XOR operation was also performed with key structures, and each stage was passed through the s-box structure (Alexan et al. 2023b). Gupta et al. They worked on a new image encryption algorithm that combines encryption methods and watermarking technique. This proposed method uses DWT-based watermarking, chaotic map, and crossover operations. With this study, images were effectively encrypted (Gupta et al. 2023). Zhu et al. They developed a new chaotic image encryption scheme using DNA coding and a fish shoal optimization algorithm, specifically to prevent differential attacks. Additionally, large keys were used in this study. This has made the algorithm more powerful, especially against differential attacks (Zhu et al. 2023). Huang et al. To develop a more effective image encryption structure, they used a different approach and hid the image to be encrypted within another image (Huang et al. 2023a). Masood et al. proposed a new image encryption scheme using chaos-based strong s-box and DNA coding together (Masood et al. 2021). Luo et al. proposed a new image encryption scheme using hyperchaotic system and particle swarm optimization (PSO) (Luo et al. 2022). Huang et al. developed a new image encryption scheme with discrete wavelet transform and compressed sensing techniques (Huang et al. 2023b). Wang et al. They developed a new image encryption algorithm using chaos, XOR, and Josephus problem (Wang et al. 2023).
The proposed algorithm makes many contributions to the literature compared to the existing works mentioned above. A new image encryption approach is proposed by using various cryptographic units together. The strong s-box structures used in this encryption algorithm are obtained uniquely. The 3 different s-box structures used here make the algorithm much more complex and powerful. With the s-box generation approach proposed in this study, more s-box structures can be generated and used in different encryption algorithms. This is one of the aspects that distinguish this work from other works. On the other hand, this study also presents a unique method for obtaining the key values to be used in the XOR operation. Thanks to this method, a different random bit sequence is used as a key for each layer of an image. This makes the encryption algorithm stronger. In addition, with the key generator method proposed here, keys can be easily generated for other encryption algorithms. Because the method used here has a very effective and simple structure. It is observed that the bit sequences obtained because of the analyses proved this by passing the NIST tests. It is shown that images can be encrypted effectively by using this s-box and key generation approaches together. Thus, significant contributions have been made to image encryption, s-box generation, and random number generator literature. Considering this point, it is hoped that this study will inspire researchers to combine different cryptographic structures and use them in different ways. In the remainder of the study, the image encryption approach proposed in the second chapter is given together with the system model and pseudocodes. In the third chapter, the key generator was first analyzed with NIST testing under subheadings to better understand the chapter. Subsequently, the proposed s-box structures were evaluated according to the most used s-box evaluation criteria in the literature and the results were compared with other studies. Finally, in this section, images encrypted with the proposed algorithm are analyzed in detail. In the fourth section, the results are discussed.
2 Proposed image encryption algorithm
The proposed image encryption algorithm is based on a strong key, XOR, random permutations, and strong s-box structures. First of all, a color image is separated into layers of red, green, and blue. These pixel values are then converted into an array. Each of these layers is XORed separately with the key value. The XOR operation is one of the structures that meet an important requirement called confusion in encryption algorithms. In addition, encryption and decryption operations are quite simple with the XOR operation. After the layers are XORed with the key, they are individually subjected to a random permutation process. The purpose of the permutation here is to meet the requirement called diffusion. In encryption algorithms, this process is usually carried out by permutation operations. After the permutation process, each layer is passed through a separate s-box structure. The aim here is to mix the data thoroughly and increase confusion. So, s-box is another important component that provides confusion like the XOR operation. A highly nonlinear s-box structure makes the algorithm extremely powerful. In the proposed algorithm, passing each layer through a different s-box structure is also one of the unique aspects of the study. In this way, a more effective confusion process is achieved. After the layers are passed through the s-box structures, the layers are combined, and the encrypted image is obtained. The basic system model of the proposed algorithm is given in Fig. 1. Decrypting the image in the proposed algorithm is quite simple. The password can be easily decrypted when the steps are applied in reverse. The layers of the encrypted image are passed through inverted s-box structures respectively. Each layer is then put into the inverse permutation process. Finally, when the decoded layers are XORed with the key value and the layers are combined, the original image is obtained.
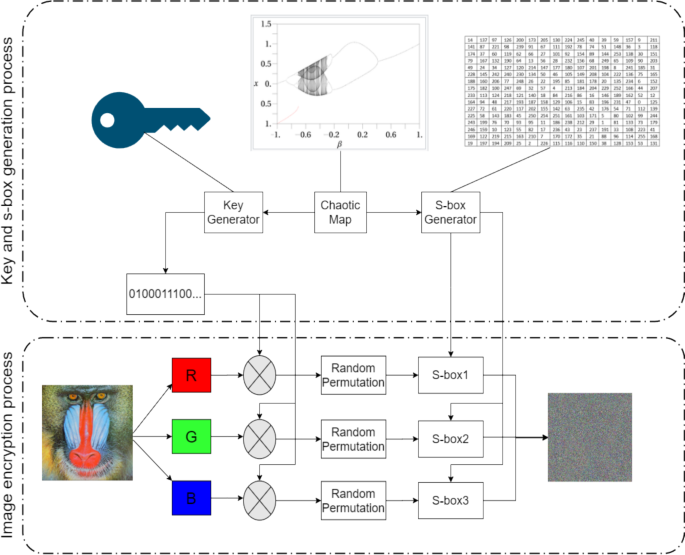
System model of the proposed image encryption algorithm
One of the most important points of this study is that both the key value and the s-box structures are obtained in a unique way using a chaotic map. For this purpose, the Gauss map was used in this study. Different maps can also be used. This is one of the rich points of the study. The mathematical structure of the Gauss map is given in Eq. (1).
A very simple and fast generator algorithm has been designed for the key generator. This generator can also be used as a random number generator in different applications. The pseudocode of the proposed generator algorithm is given in Table 1. In this algorithm, first, the initial parameters of the chaotic map are defined by the system. The values taken here were chosen randomly in the ranges where the chaotic map shows random features. It is thought that more effective results can be obtained if these values are selected with methods such as optimization in future studies. After the input parameters are defined, a random number is generated, and the chaotic map is initialized with this value. Since the images were encrypted in this study, key values were generated up to the maximum value that the pixel values could take. Therefore, the value obtained from the output of the chaotic map was first converted to an integer by multiplying it by a large number. Then, the mod256 operation was applied to the obtained value and the key value was obtained with random numbers in the range [0–256]. In this way, random number sequences of desired lengths can be generated according to the value of n. In addition, since there is no seed value in the proposed generator algorithm, a different sequence will be obtained each time it runs. In this way, it will be difficult to reproduce the series. Thus, the proposed generator is an algorithm that can be used in cryptographic applications.
S-box structures were also obtained with a similar philosophy. The pseudocode of the proposed s-box generator algorithm is given in Table 2. The s-box structures to be used here are similar to the s-box structures used in the AES algorithm. In other words, it contains 8-bit long values. Therefore, they consist of 256 values in the range [0–256]. In the proposed algorithm, the initial parameters of the chaotic map are defined as in the key generator. In this study, the initial values used to produce s-box were also chosen randomly. Selecting and analyzing the values here using different methods is one of the future studies. Choosing these initial values optimally is a hot topic that will whet the appetite of researchers. After the initial values are given, the chaotic map is initialized with a random value. When the next value is produced, this value must be multiplied by a larger number to turn it into an integer. Then, mod256 operation is applied to ensure that these values are in the [0–256] range. If this obtained value is not available in the s-box, this value is added. If this value exists in the table, it is not added, and this process continues until the table is full. In this way, a starting s-box can be easily obtained. However, the s-box structures obtained in this way show bad cryptographic properties. To improve these features, in the proposed algorithm, two values are selected with a chaotic map, and the places of these values are changed. If the nonlinearity value increases, the s-box is updated. In this way, the s-box can easily become cryptographically stronger. Here, the elements to be displaced are selected with a chaotic Gauss map. There are quite a few chaotic maps available here. The effects of other maps on the study are also one of the issues that need to be investigated for future studies.
3 Analysis results
In this study, the analysis results were examined separately in three subsections for a better understanding. In the first part, the key generator, in the second part, the s-box, and in the third part, the image encryption analysis results are given in detail.
3.1 Key generator analysis
In this study, the NIST SP 800-22 test suite was used to test whether the proposed key generator algorithm truly generates random numbers. This package consists of 15 tests in total. A p value is calculated in each of these tests. This p value is expected to be in the range [0.01–1]. As this value approaches 1, it means that the quality of the random number generator increases. For NIST SP 800-22 testing, bit sequences of approximately 1 million bits are generally used in the literature. In this study, 5 different random bit strings with a length of 1 million bits were obtained and tested. These test results are given in Table 3. As can be seen in this table, all bit sequences produced have successfully completed all test results.
3.2 S-box analysis results
Using the proposed s-box generator algorithm, 3 different s-boxes were obtained after 5000 iterations. These s-box structures are given in Tables 4, 5, and 6. Various metrics are used in the literature to evaluate the performance of an 8-bit s-box structure used in this study. The first of these is the property of bijectivity. This feature states that each value should be used only once. In this way, a more effective mixing process is achieved. Three different s-box structures obtained in this study also meet this criterion. So the suggested s-boxes are bijective. Another important criterion is SAC. This metric briefly states that; A change in the input should change almost half of the bits in the output. Therefore, this value should be 0.5 or very close to it. The averages of these values in the s-box structures proposed in this study are 0.5032, 0.5046, and 0.5095, respectively. These values show that the proposed s-boxes meet this criterion perfectly. Another and most important metric is the nonlinearity metric. Since an s-box is a nonlinear transformation, this value is expected to be high. In AES, this value is 112. In the recommended s-box structures, these values are 108, 108.5, and 108.75, respectively. These values are values that can be considered high. Another metric is BIC. Here, nonlinearity and SAC values are calculated in different ways. For this criterion, the maximum nonlinearity value is 112 and the SAC value is required to be 0.5. Recommended s-box structures where the SAC value is 0.4963, 0.4997, 0.501 respectively. Nonlinearity values are 102.29, 103.36, 103.71. SAC values are provided in the BIC criterion. However, nonlinearity values here can be increased in future studies. Finally, input–output XOR distributions are calculated. This criterion says that changes in the input must independently affect the output. It is desired that this value below. In AES, this value is highest at 4. In the s-box structures in this study, these values are 10, 10, and 12, respectively. These values are a problem in many studies and are another point that needs to be improved. In most studies, this value is calculated as 10. Therefore, these values are acceptable.
The proposed s-box structures are compared with some other studies in the literature. The comparison results are given in Table 7. The comparison is based on BIC, SAC, max XOR, and nonlinearity metrics. When the literature and Table 7 are analyzed; it is seen that the SAC value is obtained very close to 0.5 in most studies. Similarly, it is seen that the BIC-SAC value used to calculate the BIC value in these studies is close to 0.5 and the BIC-Non values are generally close to each other. In most of these studies, the max XOR value, which is the third criterion, is usually 10. This value is 4 for the s-box structure used in the AES algorithm. In other words, a value of 4 must be reached. This is one of the most prominent shortcomings of the literature. Finally, the metric focused on both in this study and most other studies is the nonlinearity value. Because an s-box structure should not have a linear structure. Therefore, researchers have been working for many years to produce s-box structures with high nonlinearity values. The main purpose of the s-box structures used in this study is to ensure that the nonlinearity value is as high as possible. Looking at Table 7, the proposed s-box structures have surpassed many studies in terms of nonlinearity values. This is one of the most important contributions of the proposed work.
3.3 Analysis results of encrypted images
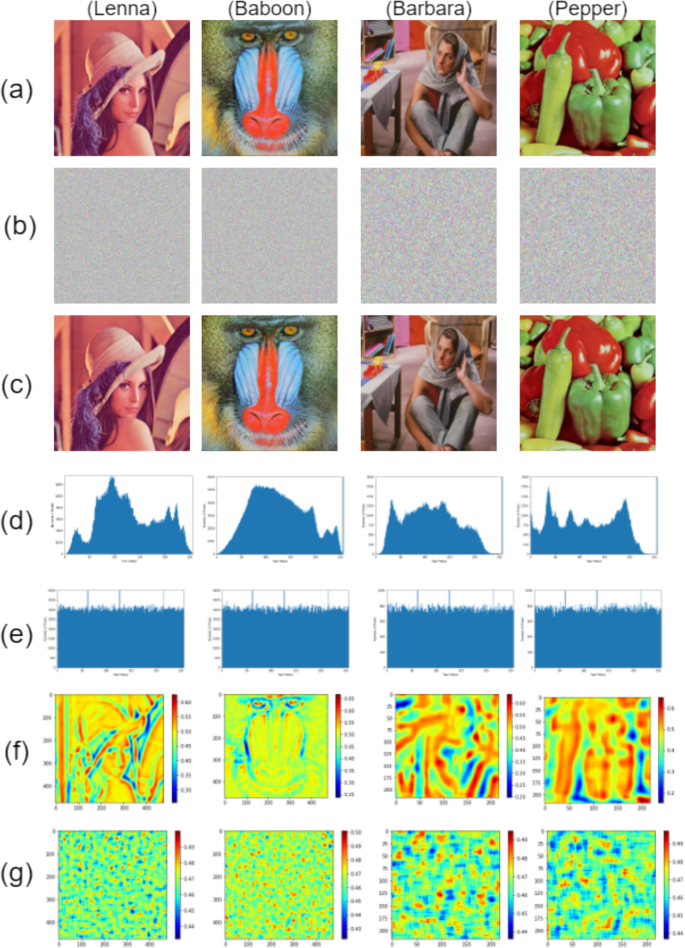
In this study, two images of 512 × 512 and 256 × 256 were encrypted and subjected to various tests. Looking at the literature, various metrics are used to analyze encrypted images. Some of these are NPCR-UACI, information entropy calculation, histogram analyses, and correlation analyses. These four criteria were examined in this study. NPCR calculates the amount of change in pixels for an encrypted image. This value is expected to be high. This value is usually expressed as a percentage. The higher this percentage, the more independent the pixels are from each other. This value is generally expected to be above 99. UACI, on the other hand, calculates the intensity of change in an encrypted image. A high UACI value indicates that most of the pixels have changed from the original image to the encrypted image. Another criterion, information entropy, calculates the distribution of the content of the image. It is calculated separately for R, G, and B channels. A higher value indicates that the image consists of more information. In a strong encryption algorithm, pixels will be distributed randomly and there will be no repetition between patterns. This value should generally be close to 8. Another criterion, histogram analysis, graphically expresses the color distribution for an image. This analysis can provide a lot of information about the image. Therefore, it is an important analysis method. Finally, correlation analysis refers to the similarity of one side of an image to the pixels on the other side. Here the result is again expressed with a graph. If this graph results in high correlation, it means there is similarity between pixels. A low correlation means that the pixels are not like each other. Histogram and correlation analysis of an encrypted image should show a uniform distribution. In this way, attackers cannot make any inferences. NPCR-UACI and information entropy values of four different images encrypted with the proposed encryption algorithm are given in Table 8. Looking at these values, the proposed method performs an effective encryption process.
The original images and their histogram-correlation graphs, their encrypted and decrypted versions, and the histogram-correlation graphs of their encrypted versions are all given in Fig. 2. When looking at this graph, it is seen that there is no relationship between the original images and the encrypted images. Especially when looking at the histogram and correlation graphs, the encrypted images have a uniform distribution. On the other hand, when looking at the histogram and correlation graphs of the original images, it seems that the images are understood. The images encrypted with the proposed method are compared with similar studies and the comparison of information entropy values for the Lenna image is given in Table 9. When we look at this table, the information entropy values are very close to the value of 8 with a value of 7.99, so it is considered successful. The comparison of NPCR and UACI values for lenna, baboon, and pepper images is given in Table 10. Looking at this table, it is seen that the NPCR value is 99% successful. Similarly, the UACI value around 0.3 is acceptable.
4 Conclusions
In this study, an innovative image encryption algorithm was designed. In the first step, the proposed algorithm XORs each layer of the image with a unique and strong new key. Then, a random permutation process is applied to each layer. Each of the encrypted layers obtained here is finally passed through a new s-box structure with a high nonlinearity value. After these processes, all layers are combined to obtain an encrypted image. Thus, XOR and s-box confusion meet the criteria, while random permutation meets the diffusion criteria. In this study, both key and s-box structures were obtained with a unique chaotic Gaussian map. The outputs of the chaotic map were converted into bit sequences and 5 different sequences with a length of 1 million were obtained. All of these arrays have successfully passed all NIST SP 800-22 tests. On the other hand, the proposed s-box structures surpassed many studies with nonlinearity values of 108, 108.5, and 108.75. With the proposed algorithm, 4 different images were successfully encrypted and the encrypted images successfully completed tests such as NPCR-UACI, information entropy, histogram analysis, and correlation analysis. As a result, it is thought that this study will make many contributions to the literature on s-box development, random number generation, and image encryption. Another important contribution of the study is to show how the important gains obtained in these fields can be used in an image encryption algorithm. At this point, both key and s-box structures can be developed with different methods. This is a promising research question and a source of motivation for the future.
