Article Content
Abstract
Background
Phishing attacks are now regarded as one of the most prevalent cyberattacks that often compromise the security of different communication and internet networks. Phishing websites are created with the goal of generating cyber threats in order to ascertain the user’s financial information. Fake websites are frequently created and circulated online, which results in the loss of essential user assets. Phishing websites can result in monetary loss, intellectual property theft, damage to one’s reputation, and disruption of regular business activities. Over the past decade, a number of anti-phishing tactics have been proposed to detect and reduce these attempts. They are still imprecise and ineffective, though. Deep Learning (DL), which can precisely learn the intrinsic features of the websites and recognize phishing websites, is one of the innovative techniques utilized to solve this issue.
Methods
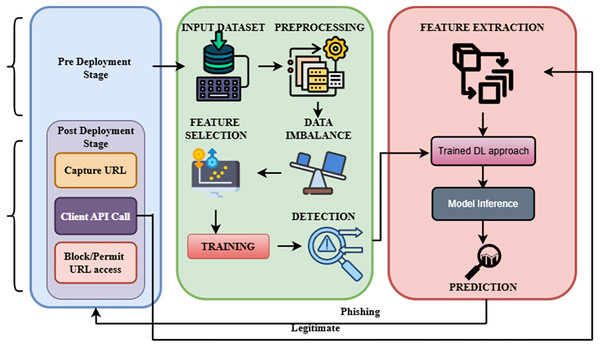
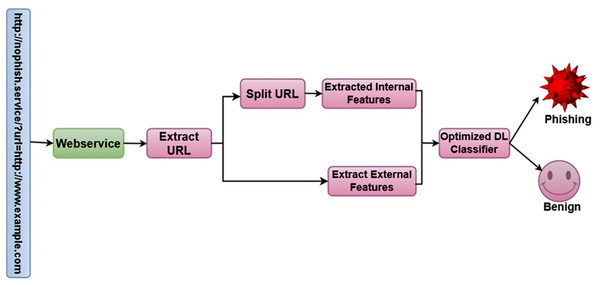
In this study, we proposed a novel OptSHQCNN phishing detection method. Pre-deployment and post-deployment are the two phases of the proposed methodology. The dataset undergoes preprocessing in the pre-deployment phase, which includes data balancing, and handling invalid features, irrelevant features, and missing values. The convolutional block attention module (CBAM) then extracts the main characteristics from web page code and linkages. The red kite optimization algorithm (RKOA) selects the significant key attributes in the third stage. The final phase involves classifying the data using the Shallow hybrid quantum-classical convolutional neural network (SHQCNN) model. To improve the effectiveness of the classification approach, the hyperparameters present in the SHQCNN model are fine-tuned using the shuffled shepherd optimization algorithm (SSOA).
Results
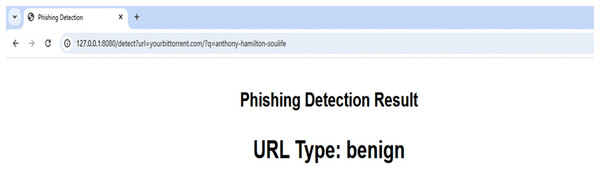
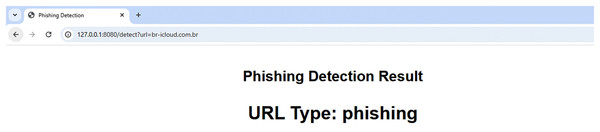
In the post-deployment phase, the URL is encoded using Optimized Bidirectional Encoder Representations from Transformers (OptBERT), after which the features are extracted. The retrieved properties are fed into a trained classifier. Next, a prediction of “phishing” or “Legitimate” is produced by the classifier. With a maximum of above 99% accuracy, precision, recall, and F1-score, respectively, the investigation’s findings showed that the suggested technique performed better than other popular phishing detection methods. The creation of a security plugin for clients, browsers, and other instant messaging applications that operate on network edges, PCs, smartphones, and other personal terminals can be aided by these findings.
Cite this as
2025. A dual-phase deep learning framework for advanced phishing detection using the novel OptSHQCNN approach. PeerJ Computer Science 11:e3014 https://doi.org/10.7717/peerj-cs.3014
Introduction
Phishing, a fraudulent practice that uses technological and social strategies to get financial and personal information from unsuspecting consumers without authorization, is still a common cybercrime (Alohali et al., 2023). One of the well-known techniques is email spoofing, which is the production of false emails with a faked origin that are frequently shared on social media sites and pose as trustworthy organizations in order to fool users into visiting phoney websites and divulging private information such as usernames and passwords (Kumar, Jaya & Rajendran, 2023; Van Geest et al., 2024; Prasad & Chandra, 2024). The risk is increased when hackers utilize devices to install malicious software, making it easier for unauthorized users to access and intercept user passwords.
Email, forums, URLs, messaging applications, text messages, and phone calls are just a few of the venues that phishers utilize to get user information (Do et al., 2024). Their fraudulent content frequently imitates authentic websites, prompting people to engage and provide personal data (Vidyasri & Suresh, 2025; Zhu et al., 2024). Financial gain or theft of identities is the primary goal of phishing, which disrupts businesses all around the world (Hendaoui & Hendaoui, 2024).
One significant non-profit organization that collects, analyzes, and disseminates information on global phishing activities is the Anti-Phishing Analysis Group. With over 300,000 phishing attempts documented in July 2023, the spike in phishing attempts from 2022 to 2023 emphasizes the need for cyber security procedures (Bozkir, Dalgic & Aydos, 2023; Asiri et al., 2024; Butt et al., 2023). Webmail is still a popular target, as evidenced by the sharp rise in attempts at phishing on well-known companies from 600 to 1,100 each month, highlighting the ongoing danger (Albahadili, Akbas & Rahebi, 2024). The Anti-Phishing Act of 2016 and other strict California legislation are aimed at punishing those who commit phishing attacks with penalties of up to 5 years in prison (Yamarthy & Koteswararao, 2024).
Criminals use deceptive emails to spread false information to a large audience and fabricate illegal copies of trustworthy websites and messages, particularly those from financial institutions. This phishing technique, which uses language and emblems from reliable companies, takes visitors unexpectedly and directs them to fake websites, raising the possibility of data exploitation (Nanda & Goel, 2024). Many businesses require additional technology to identify bogus URLs, even if phishing avoidance is of utmost importance. Bayesian addition regression trees (BART) and graph convolutional networks (GCN) are two deep learning (DL) techniques that have demonstrated effectiveness in detecting features in observed datasets (Das Guptta et al., 2024).
Although blocklists are the foundation of traditional URL detection, techniques such as the domain generation algorithm (DGA) have made it harder to detect malicious URLs that are not on the list. DL techniques are the subject of recent phishing detection (PD) research, using models like XGBoost for text preparation in email bodies and URLs (Sahingoz, Buber & Kugu, 2024; Roy, Kumar & Singh, 2024; Alsubaei, Almazroi & Ayub, 2024). Through the examination of email frameworks, links to websites, files, information of the sender, and metadata, extreme gradient boosting (XGBoost) effectively processes massive databases, managing noise and extracting key elements needed for effective phishing classification.
Modern processes require a shift from conventional approaches and a greater level of human involvement. Graph convolutional networks (GCN), recurrent neural networks (RNN), and artificial neural networks (ANN) are examples of modelling approaches that use robust chronological datasets to improve the effectiveness of phishing detection tools significantly (Karim et al., 2023; Shirazi et al., 2023). These neural network models are essential in the field of digital forensics because they help detect and stop phishing attempts, making the internet a safer place.
Motivation and our research contributions
Phishing attacks pose a significant threat to internet users, resulting in financial losses, data breaches, and reputational damage. Despite the increasing complexity of these attacks, many detection systems struggle to accurately identify phishing websites due to outdated methods that cannot keep up with evolving online threats. This study aims to address these challenges by using advanced deep learning techniques, such as OptSHQCNN and optimized feature extraction, to improve phishing detection accuracy. By integrating state-of-the-art algorithms and reliable datasets, the research seeks to enhance the efficiency and scalability of phishing detection systems, mitigating the risks associated with these cyber threats.
The major key contributions of this research are as follows,
-
To extract primary features, the convolutional block attention module (CBAM) is utilized to efficiently capture significant characteristics from URLs and webpage code for accurate phishing detection.
-
The red kite optimization algorithm (RKOA) is used to select the most essential features, minimizing the feature set and improving the computational efficiency of the model.
-
To classify phishing websites, a novel shallow hybrid quantum-classical convolutional neural network (SHQCNN) approach is introduced, leveraging their strengths for enhanced detection capabilities.
-
The shuffled shepherd optimization algorithm (SSOA) is utilized to fine-tune the parameters presented in the SHQCNN approach.
-
For URL encoding in the post-deployment phase, Optimized Bidirectional Encoder Representations from Transformers (OptBERT) is utilized to facilitate high-quality feature extraction that supports accurate predictions.
Organization of this research: This study is structured as follows. The relevant literature and the identified research gap are discussed in “Review of Existing Related Works”. “Overview of Proposed Methodology” explains the proposed multiple classes URL-classification method. The experimental design, findings, and comparative evaluation are covered in “Result and Discussions”. The work is finally concluded and possible future research areas are highlighted in “Conclusion and Future Scope”.
Result and discussions
The performance analysis of the proposed phishing detection method is shown in this section, with emphasis provided on important metrics, including accuracy, precision, recall, and F1-score. It highlights the efficacy of the proposed methodology and tackles phishing detection issues by contrasting the outcomes with those of current techniques. Within the framework of earlier studies, the discussion delves more into the approach’s advantages and possible enhancements. The parameter and their values are shown in Table 3.
Table 3:
| Parameters | Values |
|---|---|
| Epoch | 200 |
| Learning rate | 0.01 |
| Momentum | 0.9 |
| Decay | 10−5 |
| Batch size | 64 |
| Dropout rate | 0.5 to 0.1 |
Experimental setup
Each test was carried out on a Windows 10 computer that had an Intel Core i5 processor running at 2.60 GHz and 16 GB of RAM installed. Using TensorFlow and Keras as the main deep learning libraries, the suggested framework was put into practice using Python in the Anaconda3 environment. With a batch size of 64 and an initial learning rate of 0.001, the SSOA optimizer was used to train the model. With a patience of 200 epochs, early halting was implemented based on validation loss to avoid overfitting. A maximum of 100 epochs were used for the training process. Each dataset (ISCX-URL-2016, URL-Based Phishing Dataset, Mendeley_2020, and PhishStorm) was split into 80% training and 20% testing sets in order to assess the suggested method’s capacity for generalization. All baseline and proposed models consistently used this stratified splitting technique to ensure equitable performance comparisons under consistent experimental settings.
Description of the dataset
The ISCX-URL-2016, URL-Based Phishing Dataset, Mendeley_2020, and Phishstorm datasets were chosen due to their realistic representations of benign and phishing URLs, diversity, and extensive feature sets. They are sizable enough to ensure the efficient training and testing of deep learning models, cover a variety of phishing categories, and incorporate a broad spectrum of URL attributes. Additionally, these datasets provide comprehensive details that are necessary for accurate phishing detection, like WHOIS information and domain age.
-
ISCX-URL-2016: This dataset includes 114,400 URLs categorized as phishing, spam, malware, or vandalism. It contains features like URL length, special characters, and linguistic properties, aiding in the identification of phishing websites.
-
URL-Based Phishing dataset: From Kaggle, this dataset contains 11,054 records with 33 attributes, including URL structure and domain features. It helps distinguish between phishing and benign URLs.
-
Mendeley_2020: Divided into small (58,645 instances) and large (88,647 cases) subsets, this dataset includes 111 features per URL, including domain age, DNS records, and WHOIS information, useful for identifying phishing websites.
Phishstorm: This dataset contains 60,000 benign and 95,541 phishing URLs. It includes features like brand names, URL tokens, and HTTPS usage, offering insights into phishing tactics.
Evaluation criteria
Several efficiency metrics, including false positive rate (FPR), accuracy (A), precision (P), recall (R), and F1-score, were used to assess the efficacy of the suggested strategy.
The accuracy shows the rate at which the model correctly classifies the input URLs after training. The calculation involves dividing the total number of true positive (TP) and true negative (TN) instances by the overall amount of FP, FN, TN, and TP instances.
(23)
From the overall number of correctly predicted instances, precision provides the TP rate. By achieving high accuracy, it is feasible to show the recommended model’s great efficiency.
(24)
The recall is the total amount of TP overall expected samples. The performance of the proposed model is shown by a higher R-value close to one.
(25)
To show the expected sample proportion, the FPR employs a phishing URL. For a superior performance strategy, a low FPR close to zero is therefore necessary.
(26)
The F1-score shows the harmonic mean of P and R.
(27)
Matthew’s correlation coefficient (MCC) is utilized for datasets of varying class sizes and is considered to be balanced. MCC offers a correlation coefficient among expected and actual results.
(28)
Figure 8 displays the distribution of the main features that were taken out of the dataset. The Histogram of Extracted Features reveals developments in the frequency of variables like URL length and special characters. This provides information about feature attributes that increase detection accuracy and aids in identifying criteria that differentiate benign URLs from phishing ones. It is easier to comprehend how these features affect the model’s performance due to the histogram.
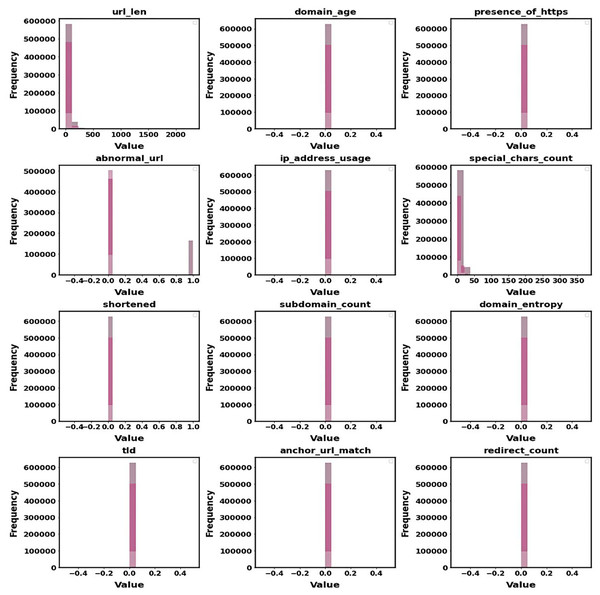
Figure 8: Histogram of extracted features.
The balanced data representation is shown in Fig. 9.
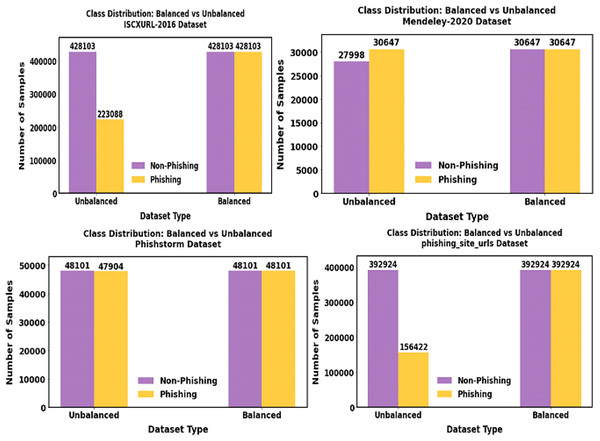
Figure 9: Shows the outcome of the balanced dataset.
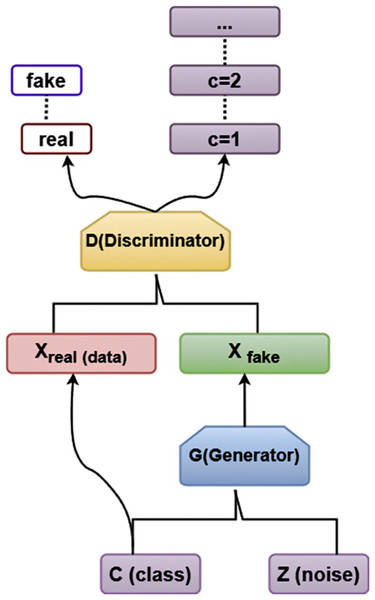
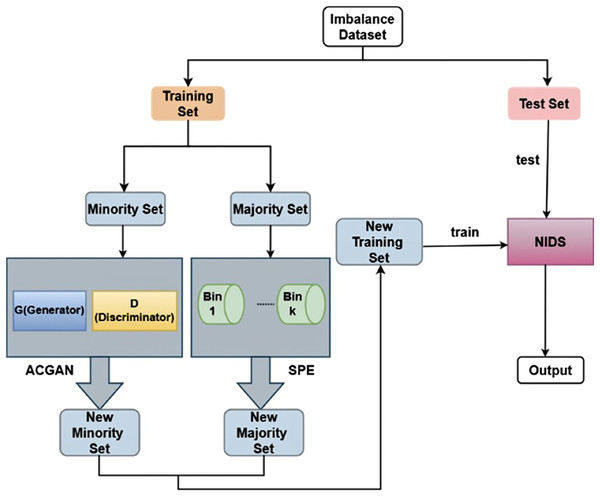
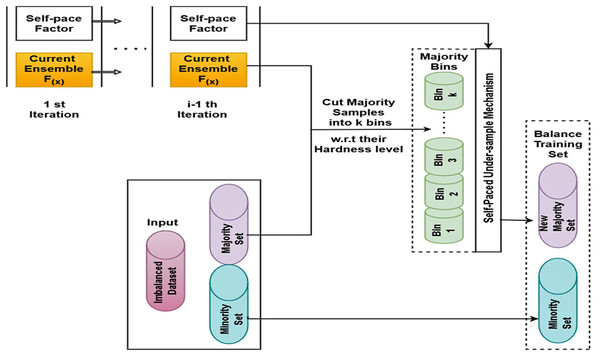
Using the data imbalance approach SPE-ACGAN approach, the minority samples present in our proposed data are balanced.
In order to qualitatively evaluate the selected URL variables, quantized DL variables for the primary phishing attack attributes that SOM reflects are displayed in Fig. 10. By assigning URLs to various sites based on each chosen rule, a qualitative depiction of the feasibility of the optimized collection of characteristics was produced.
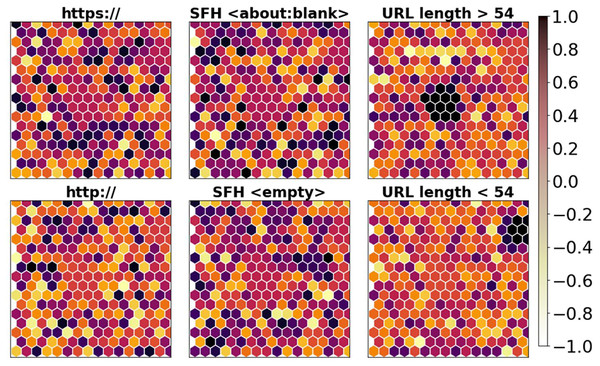
Figure 10: Visualization of selected features.
The training and testing accuracy and loss of proposed datasets are shown in Fig. 11. We trained our proposed approach over 200 epochs. The learning rate was set as 0.01.
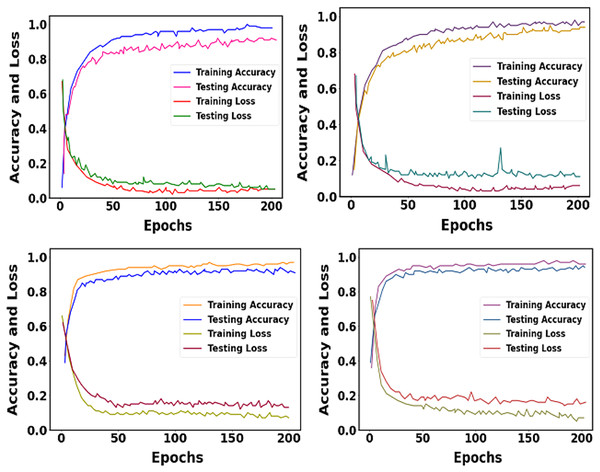
Figure 11: Graphical representation of training and testing accuracy and loss for the proposed approach.
The performance of different methods on the Mendeley_2020 dataset is displayed in Table 4, and the graphical representation is shown in Fig. 12. With 99.36% accuracy, 99.24% precision, 99.18% recall, 99.21% F1-score and 99.28% MCC, the suggested approach outperforms models such as Random Forest (97.15% accuracy) and DNN+LSTM (98.98% accuracy). In comparison to other models like LightGBM and Gradient Boost, it consistently produces better outcomes across all measures, demonstrating its efficacy.
Table 4:
| Approaches | Class | Pre | Rec | FS | MCC | Acc |
|---|---|---|---|---|---|---|
| Random forest | Phishing | 95.10% | 96.50% | 95.80% | 96.52% | 97.15% |
| Legimate | 96.46% | 95.80% | 96.00% | |||
| Average | 95.78% | 96.13% | 95.90% | |||
| Bagging | Phishing | 95.30% | 94.50% | 94.90% | 95.55% | 95.78% |
| Legimate | 96.30% | 95.30% | 95.60 | |||
| Average | 95.80% | 94.93% | 95.33% | |||
| GradientBoost | Phishing | 92.50% | 94.00% | 93.25% | 94.33% | 95.37% |
| Legimate | 93.62% | 93.16% | 93.39% | |||
| Average | 93.06% | 93.58% | 93.32% | |||
| LightGBM | Phishing | 95.00% | 95.50% | 95.25% | 95.92% | 96.67% |
| Legimate | 95.50% | 95.06% | 95.11% | |||
| Average | 95.08% | 95.28% | 95.18% | |||
| DNN | Phishing | 91.00% | − | 91.50% | 91.26% | 91.13% |
| Legimate | 91.78% | − | 91.14% | |||
| Average | 91.39% | – | 91.39% | |||
| DNN+LSTM | Phishing | 99.10% | 98.95% | 98.99% | 98.98% | |
| Legimate | 98.88% | 99.04% | ||||
| Average | – | 98.99% | 99.01% | |||
| RNN | Phishing | − | − | 97.35% | 97.26% | 97.22% |
| Legimate | − | − | 97.25% | |||
| Average | – | – | 97.30% | |||
| CNN | Phishing | − | − | 93.20% | 93.36% | 93.33% |
| Legimate | − | − | 93.59% | |||
| Average | – | – | 93.39% | |||
| Proposed | Phishing | 99.20% | 99.10% | 99.15% | 99.28% | 99.36% |
| Legimate | 99.28% | 99.26% | 99.27% | |||
| Average | 99.24% | 99.18% | 99.21% |
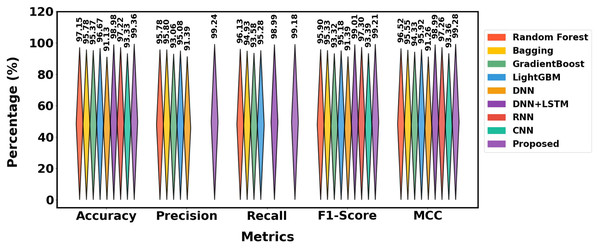
Figure 12: Differentiation of Mendeley_2020 dataset.
The ISCX-URL dataset is used in Table 5 to compare how well various strategies work. With 99.18% accuracy, 99.06% prec, 99.01% rec, 99.03% FS and 99.10%MCC, the suggested approach performs better than any other.
Table 5:
| Approaches | Class | Precision | Recall | F1-score | MCC | Accuracy |
|---|---|---|---|---|---|---|
| Auto encoder-DNN | Phishing | 90.30% | 91.50% | 90.90% | 92.11% | 92.77% |
| Legimate | 89.70% | 91.20% | 91.00% | |||
| Average | 90% | 91.36% | 91.45% | |||
| PDSMV3-DCRNN | Phishing | 99.05% | 99.20% | 99.12% | 99.05% | 99.08% |
| Legimate | 98.90% | 98.90% | 98.95% | |||
| Average | 98.98% | 99.05% | 99.03% | |||
| Variational auto encoder-DNN | Phishing | 97.10% | 97.70% | 97.40% | 97.67% | 97.89% |
| Legimate | 97.30% | 97.40% | 97.50% | |||
| Average | 97.20% | 97.54% | 97.45% | |||
| Sparse auto encoder-DNN | Phishing | 93.60% | 94.10% | 93.85% | 95.34% | 95.83% |
| Legimate | 94.00% | 94.50% | 94.30% | |||
| Average | 93.82% | 94.81% | 94.85% | |||
| Proposed | Phishing | 99.10% | 99.15% | 99.12% | 99.10% | 99.18% |
| Legimate | 99.02% | 98.90% | 99.00% | |||
| Average | 99.06% | 99.01% | 99.03% |
It outperforms models such as Sparse AE-DNN and AE-DNN and produces better results than PDSMV3-DCRNN (accuracy of 99.08%) and VAE-DNN (accuracy of 97.89%). This indicates that the proposed strategy offers the best accuracy and a well-balanced performance in terms of F1-score, precision, and recall. Figure 13 shows the differentiation of various methods using the ISCX-URL dataset.

Figure 13: Differentiation of ISCX-URL dataset.
The URL dataset is used in Table 6 to compare the effectiveness of different strategies. The proposed approach achieves the best results across all parameters, outperforming all current models with 99.12% accuracy, 99.04% precision, 99.02% recall, 99.03% F1-score and 99.08% MCC. While LR+SVC+DT (98.12% accuracy) and RF (96.77% accuracy) perform well, they are still inferior to the proposed approach. The proposed method is more effective in terms of precision and recall than SVM, which performs lowest with an accuracy of 71.8%. Figure 14 illustrates the distinction of various methods employing the URL dataset.
Table 6:
| Approach | Class | Prec | Rec | FS | MCC | Acc |
|---|---|---|---|---|---|---|
| DT | Phishing | 95.5% | 96.4% | 95.80% | 95.66% | 95.41% |
| Legimate | 96.1% | 95.6% | 96.02% | |||
| Average | 95.8% | 96% | 95.91% | |||
| LR+SVC+DT | Phishing | 97.60% | 95.80% | 95.90% | 96.98% | 98.12% |
| Legimate | 97.02% | 96.86% | 95.88% | |||
| Average | 97.31% | 96.33% | 95.89% | |||
| SVM | Phishing | 96.80% | 48.00% | 65.90% | 68.60% | 71.8% |
| Legimate | 95.88% | 51.62% | 65.44% | |||
| Average | 96.34% | 49.81% | 65.67% | |||
| RF | Phishing | 96.60% | 97.90% | 97.20% | 96.94% | 96.77% |
| Legimate | 96.86% | 97.12% | 97.04% | |||
| Average | 96.73% | 97.51% | 97.12% | |||
| Proposed | Phishing | 99.00% | 99.10% | 99.04% | 99.08% | 99.12% |
| Legimate | 99.08% | 98.94% | 99.02% | |||
| Average | 99.04% | 99.02% | 99.03% |
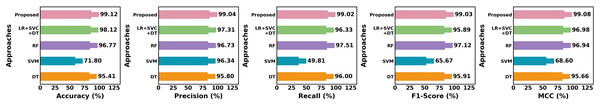
Figure 14: Differentiation of URL dataset.
The performance of different methods on the Phishstorm dataset is contrasted in Table 7. According to all criteria, the proposed strategy performs best, achieving 99.17% accuracy, 99.10% recall, 99.06% precision, 99.08% F1-score and 99.12% MCC. With 97.10% and 95.05% accuracy, respectively, Texception Net and GA perform well in comparison, although they are still not as good as the proposed strategy. LSTM and CNN perform worse, especially in recall and precision. The performance of the Phishstorm dataset is shown in Fig. 15.
Table 7:
| Methods | Class | Recall | Precision | F-score | MCC | Accuracy |
|---|---|---|---|---|---|---|
| CNN | Phishing | 85.00% | 86.80% | – | 87.85% | 90.16% |
| Legimate | 83.24% | 84.50% | – | |||
| Average | 84.12% | 85.65% | – | |||
| LSTM | Phishing | – | 85.10% | – | 86.06% | 87.77% |
| Legimate | – | 83.70% | – | |||
| Average | – | 84.40% | – | |||
| URLNet | Phishing | – | 89.40% | 88.74% | 90.81% | 93.95% |
| Legimate | – | 87.88% | 87.03% | |||
| Average | – | 88.64% | 87.89% | |||
| CNN-LSTM | Phishing | 87.30% | 88.60% | 87.94% | 90% | 92.29% |
| Legitimate | 86.50% | 87.10% | 86.80% | |||
| Average | – | 87.85% | – | |||
| Texception net | Phishing | 88.90% | 92.80% | 90.81% | 93.52% | 97.10% |
| Legitimate | 87.40% | 91.74% | 89.61% | |||
| Average | 88.15% | 92.27% | 90.21% | |||
| GA | Phishing | 90.40% | 94.10% | 92.20% | 93.35% | 95.05% |
| Legitimate | 89.84% | 92.54% | 91.24% | |||
| Average | 90.12% | 93.32% | 91.72% | |||
| Proposed | Phishing | 99.10% | 99.20% | 99.15% | 99.12% | 99.17% |
| Legitimate | 99.02% | 99.00% | 99.01% | |||
| Average | 99.06% | 99.10% | 99.08% |
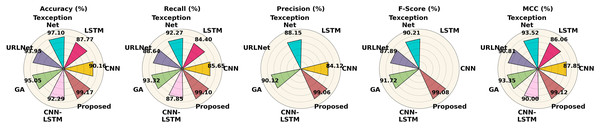
Figure 15: Performance differentiation of various approaches using the Phishstorm dataset.
The performance of different optimization techniques is compared in Table 8 and Fig. 16, which demonstrates that the suggested optimizer performs better than the others across the board. In comparison to algorithms like Adam, Adamax, and SGD, it achieves the highest accuracy (99.28%), precision (99.16%), recall (99.24%), and F1-score (99.20%), demonstrating a greater capacity to create accurate, exact, and dependable predictions. This indicates that when it comes to handling the optimization process, the proposed optimizer provides superior overall performance.
Table 8:
| Optimizer | Accuracy | Precision | Recall | F1-score |
|---|---|---|---|---|
| Adam | 98.89% | 98.95% | 98.79% | 98.87% |
| Adagrad | 58.14% | 75.52% | 55.28% | 62.10% |
| Adamax | 98.22% | 98.44% | 98% | 98.22% |
| SGD | 82.65% | 86.30% | 80.14% | 82.59% |
| Nadam | 98.81% | 98.85% | 98.66% | 98.75% |
| RMSprop | 98.27% | 98.35% | 98.12% | 98.24% |
| Proposed | 99.28% | 99.16% | 99.24% | 99.20% |
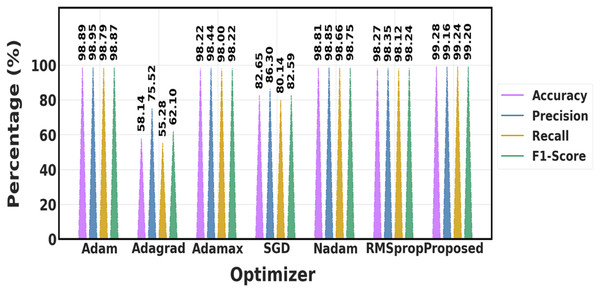
Figure 16: Comparison of various optimization approaches.
Figure 17 shows distinctions both with and without the feature selection approach. The suggested feature selection method performs better when compared to current feature selection techniques.
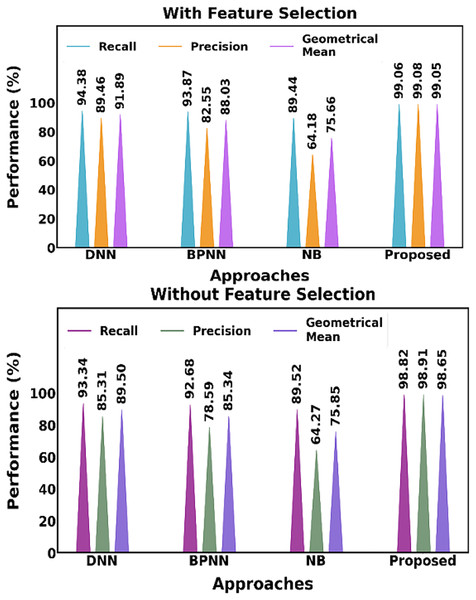
Figure 17: Distinguishing between the proposed and current methods, both including and excluding the feature selection approach.
Table 9 presents the performance of the proposed feature selection (RKOA) and optimization (SSOA) methods across four phishing detection datasets. The results demonstrate consistently high accuracy ranging from 99.12% to 99.36%, with low computational time between 9.01 ms and 13.25 ms. This highlights the effectiveness and efficiency of the proposed approach in selecting relevant features and optimizing the model.
Table 9:
| Proposed datasets | Feature selection method | Optimization approach | Accuracy | Time (ms) |
|---|---|---|---|---|
| ISCX-URL-2016 | RKOA | SSOA | 99.18% | 12.05 |
| URL based Phishing | RKOA | SSOA | 99.12% | 13.25 |
| Mendeley-2020 | RKOA | SSOA | 99.36% | 9.01 |
| Phishstorm | RKOA | SSOA | 99.17% | 10.11 |
The suggested feature extraction method is compared with the current feature extraction methods, including CNN, LSTM, CNN-LSTM, RNN, and CNN-BiLSTM. Figure 18 illustrates how the suggested model outperforms current models while producing better results.
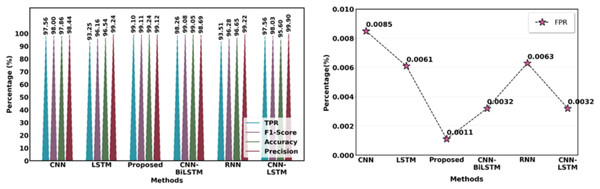
Figure 18: Comparison of suggested and current extraction of features methods.
Table 10 and Fig. 19 contrast the effectiveness of several strategies with the suggested technique in terms of the following essential metrics: F1-score, accuracy, precision, recall, MCC and false positive rate (FPR). With a low FPR (0.34%) and the maximum accuracy (99.72%), precision (99.76%), F1-score (99.54%) and MCC (99.58%), the suggested method is a very effective and dependable model. With a much lower FPR, this model offers a better balance than other models such as CNN Attention (99.31%) and faster region-based convolutional neural network (Faster RCNN) (99.68%), outperforming them in precision and recall as well as accuracy and F1-score. Models such as RNN+CNN and Bayes Net exhibit reduced accuracy and precision, underscoring the efficacy of the proposed strategy.
Table 10:
| Methods | Acc | Prec | Rec | FS | FPR | MCC |
|---|---|---|---|---|---|---|
| DNN | 99.52% | – | – | – | – | – |
| LSTM | 99.57% | – | – | – | – | – |
| CNN | 99.43% | 97% | 98.2% | 97.6% | – | 98.51% |
| Bayes Net | 92.8% | 93.4% | 90.1% | 91.7% | – | 92.24% |
| Faster RCNN | 99.68% | 99.13% | 88.67% | – | – | – |
| RNN+CNN | 95.79% | 94.24% | 97.27% | 95.73% | – | 95.76% |
| CNN attention | 97.82% | 99.74% | 98.89% | 99.31% | 0.63% | 98.56% |
| Proposed | 99.72% | 99.76% | 99.32% | 99.54% | 0.34% | 99.58% |
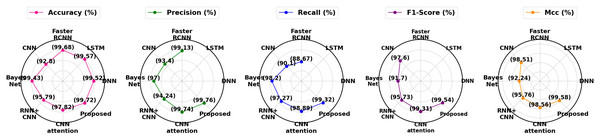
Figure 19: Overall differentiation of proposed with existing approaches.
Table 11 highlights the training and inference times of the proposed model across different phishing datasets. Training time reflects how long the model takes to learn from each dataset, while inference time indicates the speed at which it predicts outcomes per sample. The results show that the model maintains low inference times under 1.1 ms, demonstrating its suitability for real-time phishing detection.
Table 11:
| Dataset | Training time (s) | Inference time (ms) |
|---|---|---|
| ISCX-URL-2016 | 125.4 | 1.02 |
| URL-based phishing | 196.8 | 0.96 |
| Mendeley-2020 | 194.2 | 0.89 |
| PhishStorm | 202.6 | 0.93 |
Ablation study
We performed ablation research by gradually deleting or replacing essential components in order to assess the contributions of each component in our phishing detection framework. The impact of each element on overall performance, including accuracy, precision, recall, and F1-score, is investigated in this study.
The incremental impact of different phishing detection pipeline components across four distinct datasets is shown in Table 12. The more steps that are added to the process, the more accurate it becomes. First, preprocessing produces high accuracy in every dataset. Performance is significantly improved by adding data imbalance treatment, underscoring the need to resolve class imbalances. Accuracy in feature extraction and selection keeps increasing, highlighting how important it is to choose the most pertinent features for phishing detection. Lastly, the most significant improvement and best accuracy are obtained with the addition of classification and URL encoding. This demonstrates how every stage helps to improve the model’s capacity to recognize phishing URLs with accuracy.
Table 12:
| Methods | Dataset 1 | Dataset 2 | Dataset 3 | Dataset 4 |
|---|---|---|---|---|
| Preprocessing | 98.72% | 98.83% | 99.01% | 98.56% |
| Preprocessing + data imbalance | 98.96% | 98.95% | 99.03% | 98.72% |
| Preprocessing + data imbalance + Feature extraction | 99.04% | 98.99% | 99.08% | 98.99% |
| Preprocessing + data imbalance + Feature Extraction + Feature selection | 99.12% | 99.08% | 99.15% | 99.07% |
| Preprocessing + data imbalance + Feature Extraction + Feature selection + Classification | 99.21% | 99.12% | 99.18% | 99.24% |
| Preprocessing + data imbalance + Feature Extraction + Feature selection + Classification URL encoding | 99.45% | 99.28% | 99.30% | 99.28% |
Discussions
A crucial cybersecurity tactic is phishing detection, which aims to spot and stop fraudulent efforts to steal private data by impersonating trustworthy organizations. As phishing websites and emails have become more prevalent, sophisticated detection methods like machine learning and deep learning are being used to protect users from economic and reputational damage.
Existing limitations
While applicable in certain situations, current phishing detection techniques have a number of significant drawbacks. The accuracy of phishing detection is increased by hybrid models such as DNN-LSTM, which combine character-based connections with high-level NLP characteristics. However, they are not appropriate for real-time applications due to their computational complexity. Similar to this, CNN-based methods have limited scalability since they rely on particular kernel variants, which limits their capacity to adapt to a variety of datasets despite being lightweight and successful in feature selection. Although they have domain-specific advantages, novel approaches like the binary bat algorithm and LBPS with BP neural networks struggle with generalizability and broader applicability. Moreover, hybrid feature-based techniques such as PDHF include delays that are inappropriate for time-sensitive situations while optimizing accuracy in the order of computing overhead.
Overcoming limitations with the proposed method
The novel two-stage methodology of the proposed OptSHQCNN architecture successfully addresses these issues. The robustness of feature selection is increased during the pre-deployment phase by thorough preprocessing, which removes invalid and unnecessary features, and the CBAM, which isolates crucial properties. The complexity seen in hybrid models is reduced using the RKOA, which guarantees a computationally effective selection of essential features. In order to improve scalability and applicability across a variety of datasets, OptBERT’s integration for URL encoding after deployment guarantees that the model preserves significant contextual information. By further optimizing classification and lowering computational costs, SHQCNN can be fine-tuned using SSOA to improve real-time performance.
A thorough validation process was carried out using four different benchmark datasets: ISCX-URL-2016, URL-Based Phishing Dataset, Mendeley_2020, and PhishStorm in order to guarantee the stability and generalizability of the proposed OptSHQCNN model. We are able to show the adaptability of our feature selection and optimization techniques in a variety of data settings because these datasets vary in terms of structure, source, and distribution. RKOA and SSOA integration maintained stability in classification metrics across datasets while also ensuring effective feature reduction. The framework also exhibits great potential for real-time implementation in browser-based and edge-security applications by reducing computing overhead and utilizing effective encoding with OptBERT, making it scalable to massive data quantities.
Benefits of the proposed method
Compared to current approaches, the OptSHQCNN framework has the following benefits:
-
High accuracy and efficiency: Over 99% accuracy, precision, recall, and F1-score are attained by combining sophisticated feature extraction and selection approaches.
-
Reduced computational complexity: The model’s operations are streamlined by optimization methods such as RKOA and SSOA, which qualifies it for real-time detection scenarios.
Scalability and adaptability: The model may generalize over a variety of datasets by utilizing OptBERT for URL encoding, which overcomes the drawbacks of domain-specific methods.
-
Effective feature selection: By ensuring that only the most pertinent features are taken into consideration, the CBAM model lowers noise and improves classification results.
-
Broad applicability: The two-stage framework can be expanded to a number of real-world uses, including personal terminals, network edges, and browser plugins.
Proposed limitations
Our proposed method performs better than current approaches and produces outstanding outcomes, according to testing and evaluation. However, the suggested system does have several drawback. The model does not determine whether the website is live by looking at its URL, which affects the findings. In order to get around this restriction, we might need to enhance feature engineering and speed up the training process. This would enable us to confirm the website’s current status and increase the correctness of the training process.
Conclusion and future scope
In order to tackle the crucial problem of phishing detection, the proposed investigation presents OptSHQCNN, an effective and novel two-stage deep learning architecture. In order to ensure thorough data handling and feature analysis, the methodology is divided into pre-deployment and post-deployment phases. Data imbalances, irrelevant features, and missing values are efficiently managed by pre-deployment preprocessing, and the convolutional block attention module (CBAM) precisely improves feature extraction. The red kite optimization algorithm (RKOA) increases model efficiency by making sure that only essential features are chosen. By fine-tuning hyperparameters with the shuffled shepherd optimization algorithm (SSOA), the shallow hybrid quantum-classical convolutional neural network (SHQCNN) improves classification accuracy even more. Post-deployment URL encoding using Optimized Bidirectional Encoder Representations from Transformers (OptBERT) enhances feature representation and classification by capturing the complex patterns of phishing URLs.
The results, which showed over 99.72% accuracy, 99.76% precision, 99.32% recall, 0.34% FPR and 99.54% F1-score, demonstrate the effectiveness that the proposed structure performs in comparison to current techniques. Numerous benefits arise from the model’s capacity to incorporate advanced deep learning and optimization methodologies. It provides great dependability by reducing false positives and negatives. Scalability and adaptation to various datasets and phishing scenarios are made feasible by the modular two-stage architecture. OptBERT’s contextual encoding ensures improved identification of intricate phishing URLs, while quantum-inspired SHQCNN speeds up computations without impacting accuracy. These additions enable the framework to be used in real-world applications like browser plugins and instant messaging app integrations, promoting safer online spaces and serving as a standard for phishing detection research in the future. While this study emphasizes URL-based feature extraction due to its suitability for real-time detection, it acknowledges the limited consideration of other informative aspects, such as the visual similarity of web content and user interaction behaviour. Incorporating these features in future work may further enhance the model’s performance in complex and deceptive phishing scenarios.
Additional Information and Declarations
Competing Interests
The authors declare that they have no competing interests.
Data Availability
The following information was supplied regarding data availability:
The data is available at Figshare.
Yamarthi, Dr. Narasimha Rao (2025). Advanced Phishing Detection. figshare. Dataset. https://doi.org/10.6084/m9.figshare.28130225.v1.
Funding
The authors received no funding for this work.